2025 Printable Template
This website is not affiliated with any government agency or tax authority.
Form last updated: 03/2024. Please verify this is the current version before use.
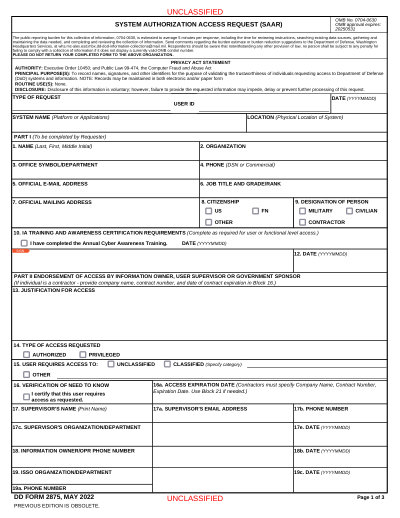
Easily complete & submit your DD 2875 form
Follow these simple steps to fill, sign, and send your DD 2875 form online.
Fill out your form
Our user-friendly editor helps you quickly enter personal & business details in the DD 2875 template.
Sign the form
Add your electronic signature to the fillable DD 2875 form to certify it came directly from you.
Send it to the requester
Download and instantly print or share your signed DD 2875 with the requester.
How to fill out a DD 2875 online?
Follow these steps to complete your DD 2875 form online.
Step 01
Read the instructions thoroughly to understand the required information.
Step 02
Complete all necessary fields with accurate details.
Step 03
Review the form to ensure all required sections are filled out.
Step 04
Consult guidelines for signature requirements and sign if needed.
Step 05
Save a copy for your records after completion.
Step 06
Submit the form to the appropriate authority as directed.
What is a DD 2875 used for?
Who needs to fill out a DD 2875 form
What is Form DD 2875?
Who approves Form DD 2875?
Can Form DD 2875 be used for multiple systems?
Ready to Fill Your Form DD 2875?
Start filling out your form online in minutes. Fast, secure, and completely free.
Our users speak for themselves
Exceptional quality verified by real professionals.
"The folks at PDFocused were just wonderful at helping me resolve a very important issue. I would highly recommend them because there is someone actually paying attention and reaching out to help those who use their service!"
Eugene
Mar 20, 2026
"I wanted to convert a PDF quickly and this tool made it very easy. Everything worked great, and I didn't have to deal with any confusing process."
Bosmat Shelef
Feb 4, 2026
"I needed to convert a PDF quickly and this tool made it easy. Everything worked as expected and I didn't have to deal with any confusing steps."
Elibz
Feb 4, 2026
"Super great and easy to use"
Drew Mascia
Feb 28, 2026